6 elements that every penetration test report must have

Important disclaimer - it is very important that you vet the report template with the customer before you start the engagement. It is important so that they can suggest any changes ahead of the chaos.
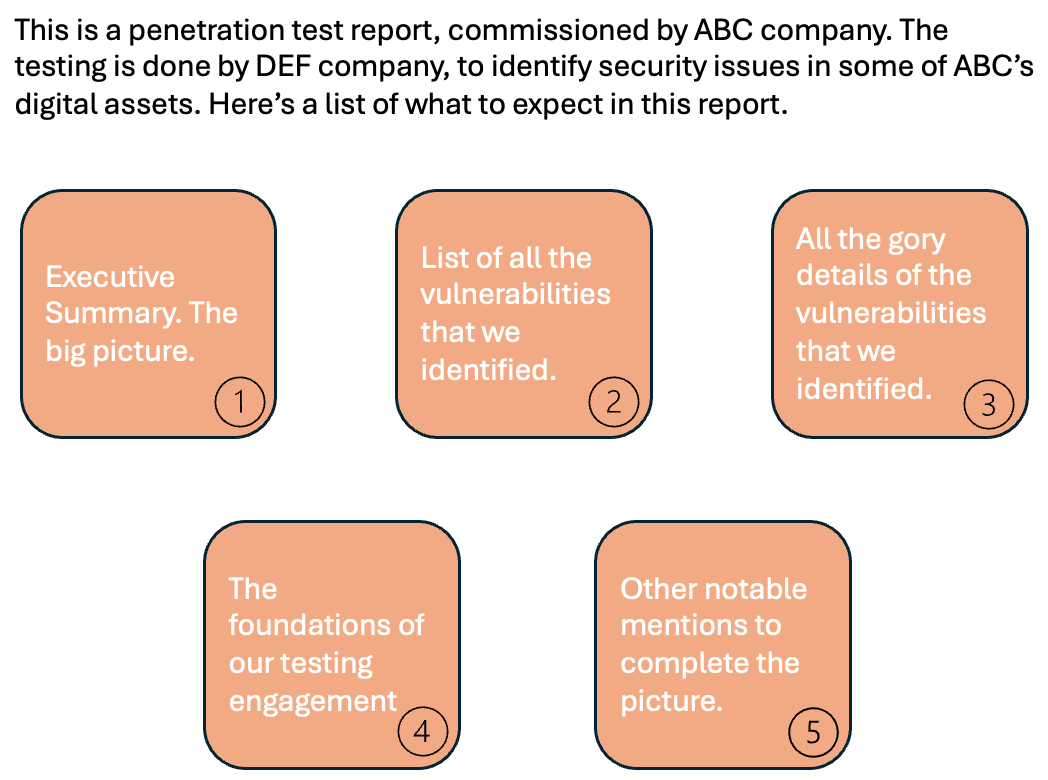
So here are the most important elements of a pentest report, in that order,
Introduction
What is this document
How to read this report
Here's an example.
Executive summary
you get two types of customers in every engagement. One who implements your recommendation, and another one who pays for the pentest. This summary is for the one who pays. Make it count.
kill chain/ attack-narrative Infographic, key risks, impact, high level recommendations, potential timelines (if possible).
Leaders want to know the key risks and the exposure (e.g., potential fine from regulator, reputation risk, risk of non-compliance, etc.).
with each key risk, link all different vulnerabilities that are part of that risk
No details, but lot of references to locations (in the current report) where the finding is detailed.
It will be better if this part of report is printed and hand-delivered to the customer.
Table of Findings
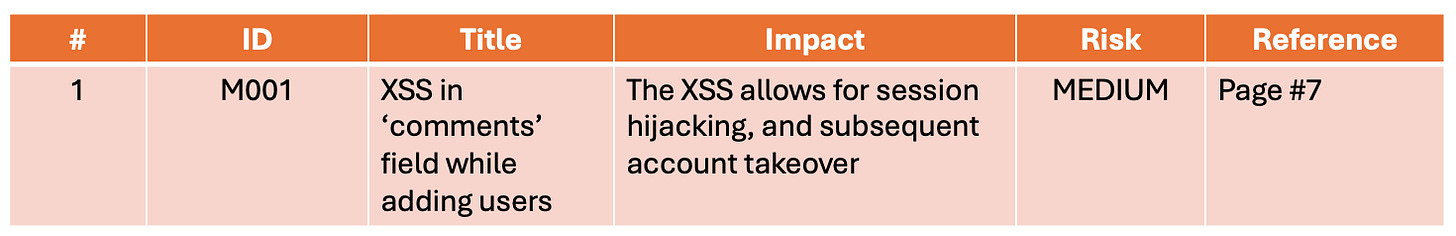
usual suspects to go here (#, ID, title, small description with impact, risk rating, reference to the location in current document). Here's an example.
Detailed Findings
Some ppl include attack narratives here, others add one table per finding, divided by severity/ risk levels. At the minimum, each finding should have the following fields
finding ID (also see 'table of findings' above).
severity/ risk
finding title (should combine vulnerability and impact)
finding details (should explain vulnerability, impact, and justification for severity/ risk rating)
remediation
other info for compliance purposes (e.g., CWE ID, any CVE ID, OWASP TOP-10/ ASVS/ Testing Guide reference). Many regulations expect this information to be present for each vulnerability. Not including this information may result in an audit finding.
Scope, Methodology
why is this at the end?
Becoz it doesn’t matter much, at least for the report. It is discussed, agreed upon, and approved much prior to the report. It is kept in report for record purposes and for the first type of customer (refer executive summary).
Sure, someone may want to check the coverage. However, overall, the most important items for customer are already described above.
Other relevant Annexure
Output from automated tools like Nessus, nmap, burp suite, sqlmap, etc.
Criteria for severity/ risk ratings (why a vulnerability/ risk is 'high', 'medium', or 'low', etc.)
Some elements that I have not included here, but are assumed to be present, are: -
Cover page, logo,
document title, client name (name, email ID of the point of contact)
document control (who created/ when, who approved/ when, change tracker)
vendor contact details
Additional Guidance
Pentest-Tools.com on LinkedIn: 10 things NOT to do in your pentest reports: ❌ Give generic…
Pro tips from 10 ethical hackers for stellar reports
Penetration testing reports: A powerful template and guide
Your Reporting Matters: How to Improve Pen Test Reporting - Black Hills Information Security
Reporting for Pentesters with BB King - Antisyphon Training
Sign up for Risky Context
I write at the intersection of pentest, auditing, risk management and career advice. I add context to the infosec risk. I help answer the question 'where is the risk?'
No spam. Unsubscribe anytime. Musings based on real experiences, not theory. All Infosec, mashed up.
At the intersection of pentest, auditing, risk management and career advice. Musings based on real experiences, not theory. All infosec, mashed up.
Follow the Risky Context channel on WhatsApp (if WhatsApp is your thing. Your number is not shared with others when you connect to my channel): https://whatsapp.com/channel/0029VaDqrFU8aKvQohD5nq0r